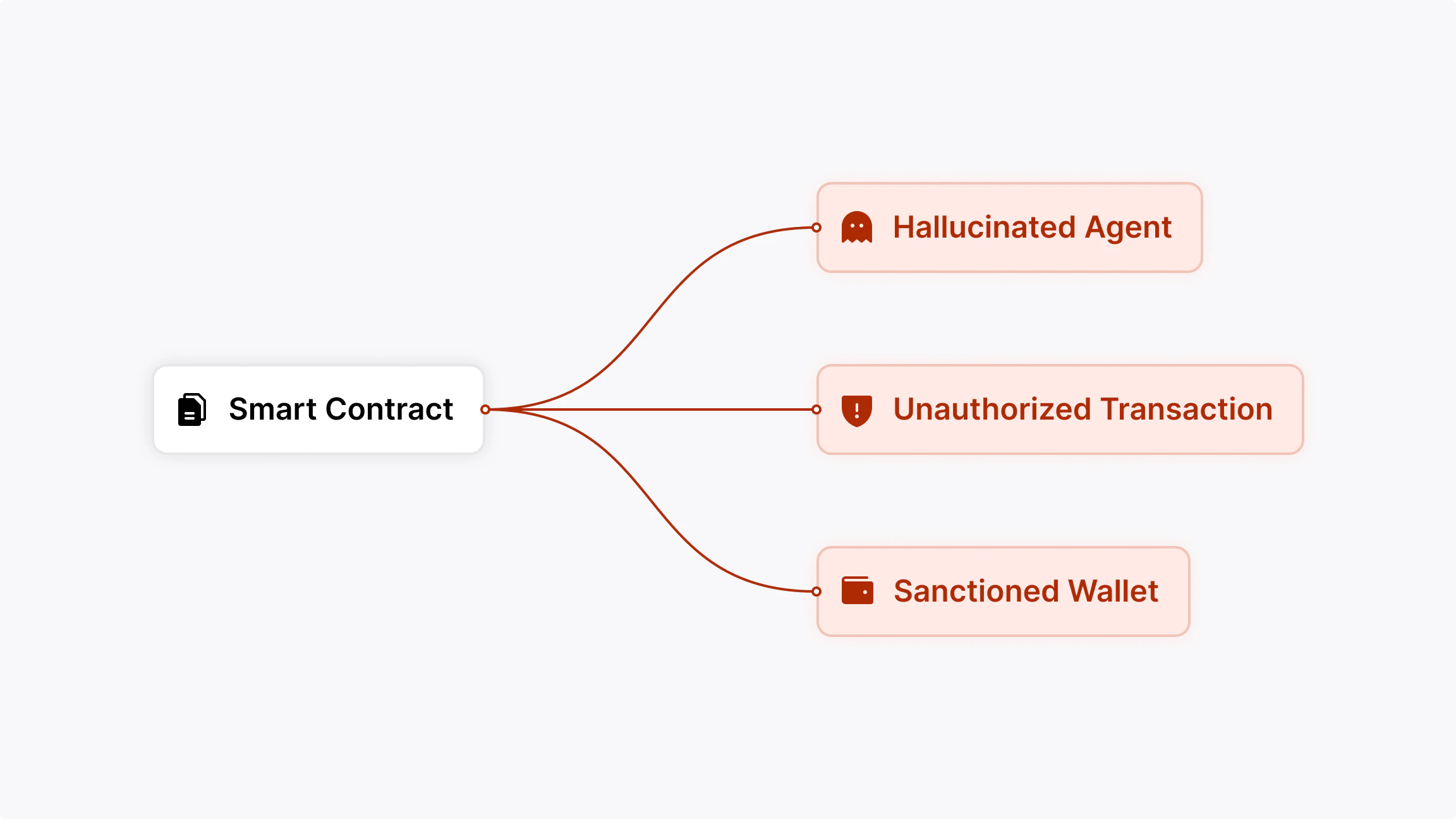
The problem
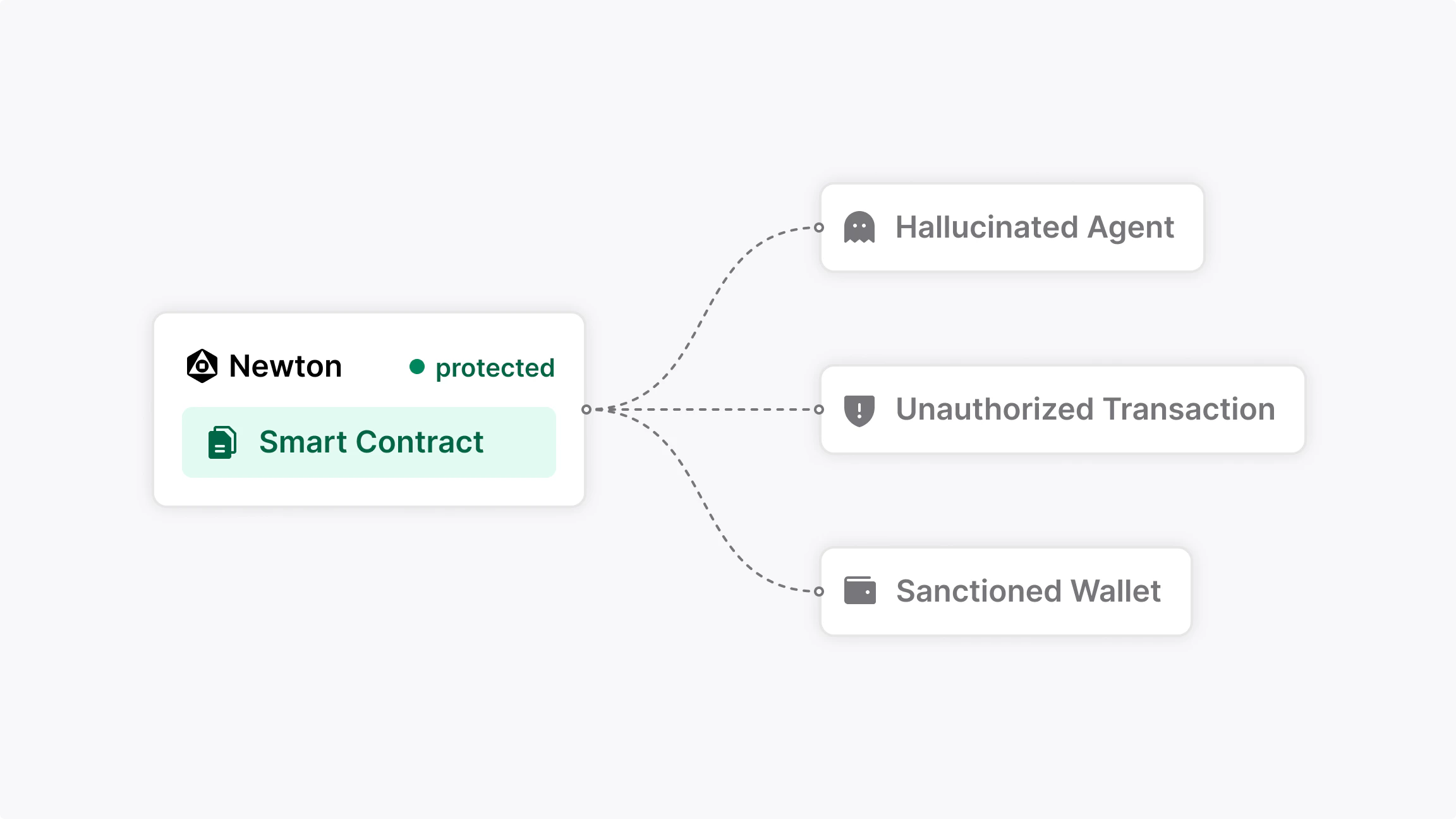
The solution
Modular and chain-agnostic
Newton integrates with most EVM-compatible networks including Ethereum, Base, and Arbitrum. Non-EVM support is on the roadmap.Try the demo
See a live example of a Newton-powered sanctions-checked transfer app
Talk to an expert
Get in touch to discuss your integration or partnership opportunity
What it looks like
Quickstart
Run this example end-to-end in 5 minutes
Walkthrough
Why Newton
- Verifiable Trust: Every compliance decision is backed by a BLS attestation, not reputation.
- Privacy-Preserving: Only hashes and commitments are onchain — no PII or sensitive data exposure. See the privacy layer.
- Composable: Works with wallets, dApps, AI agents, and DeFi protocols through a standard SDK interface.
- Chain-Agnostic: Newton proofs can be verified across any supported EVM chain via lightweight verifier contracts.
- Extensible: Supports both open-source policies and enterprise modules for regulated financial institutions.
Next Steps
Quickstart
Simulate your first policy evaluation in 5 minutes
Core Concepts
Understand policies, intents, tasks, and attestations